Ghost SIMs are mobile numbers issued on stolen or forged KYC documents that are used to receive OTPs, activate fraud bank accounts, and funnel stolen funds. PoS (Point of Sale) agents at telecom and banking outlets are often bribed or coerced into issuing these SIMs or activating fraudulent accounts — creating the invisible backend of organised cyber fraud in India.
Introduction
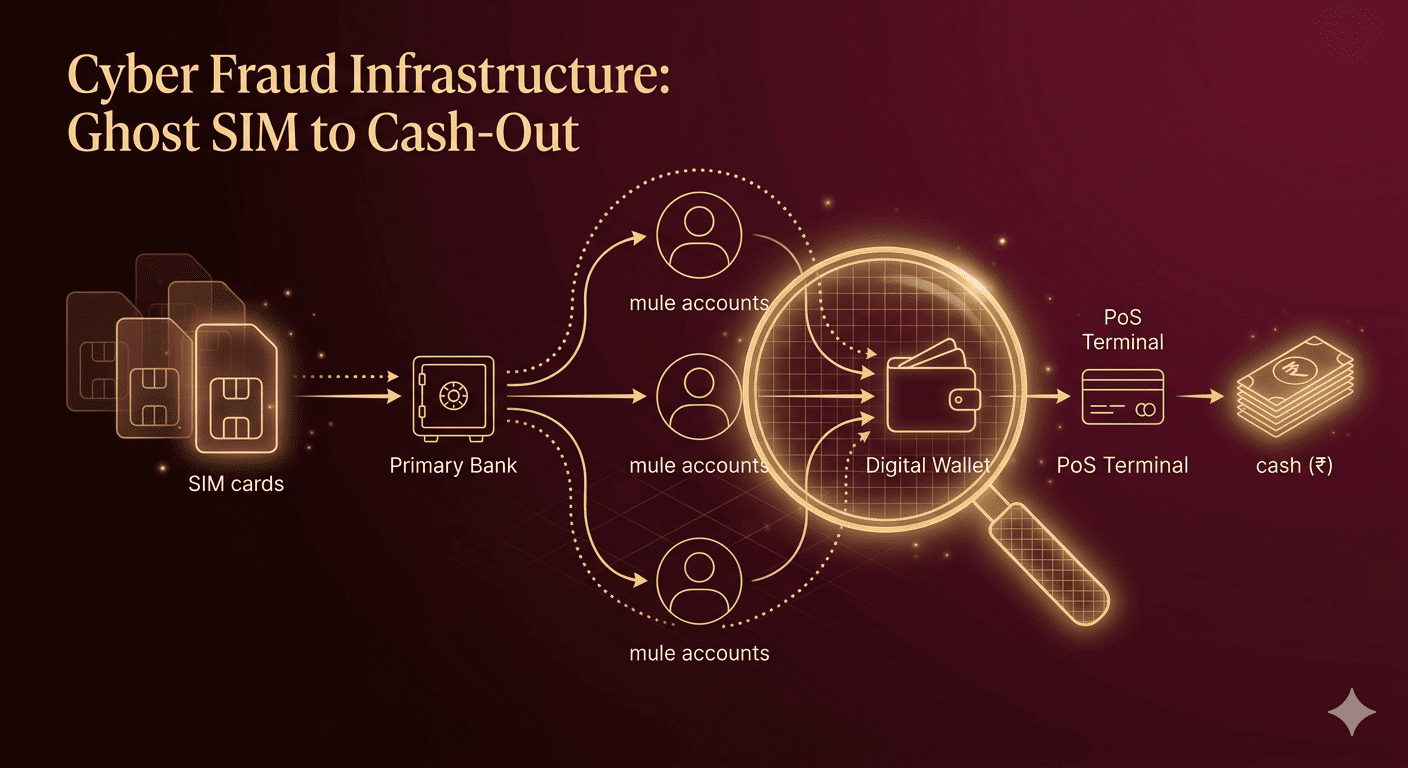
When a victim reports Rs 8 lakh stolen from their account, investigators often trace the funds through a chain: victim’s bank account → mule account 1 → mule account 2 → a ‘ghost’ SIM-linked wallet → withdrawn at a PoS terminal in Rajasthan or Jharkhand.
The ghost SIM and rogue PoS agent ecosystem is the unsexy, unglamorous backend of India’s cyber fraud machinery — and it is the reason why so many fraud cases go unsolved. Without ghost SIMs to receive OTPs and PoS agents to cash out, the entire fraud network collapses.
This technical guide exposes how the ghost SIM and PoS fraud chain works end to end, identifies the states most involved, examines what banks and NPCI are doing to detect it, and gives merchants a practical checklist to avoid becoming unwitting participants. [timesnownews]
What Is a Ghost SIMs?
A ghost SIMs is a mobile SIM card issued on fraudulently obtained or forged KYC documents. The real person whose Aadhaar or Voter ID was used to issue the SIM is unaware it exists. The SIM is controlled entirely by the fraudster and is used for one purpose: receiving OTPs and verification messages for fraudulent banking and UPI transactions.
Example: A cybercrime cell in Rajasthan found that a single local resident’s Aadhaar had been used to register 47 SIM cards across 6 telecom operators — all linked to fraud UPI accounts and mule bank accounts.
How Ghost SIMs + PoS Agent Fraud Works: Step by Step
- KYC data is obtained — from data leaks, fraudulent telecom retailers, or bribed bank staff
- Ghost SIMs are issued using forged or stolen KYC — often via rogue PoS agents at telecom outlets
- Mule bank accounts are opened using ghost SIMs numbers as the registered mobile
- Fraud proceeds are transferred to mule accounts by the primary scam operation
- OTPs for withdrawals land on ghost SIMs — fraudsters receive them in real time
- Cash-out happens at PoS terminals — agents process transactions for a 10–15% cut
- Ghost SIMs is discarded — the trail goes cold
PoS Agent’s Core Role
Point of Sale (PoS) agents, authorized by telecom providers to issue SIMs via eKYC, exploit the process by conducting a legitimate eKYC for the customer while secretly issuing a duplicate “ghost” SIM during a faked retry. They inform the customer the first eKYC failed, perform a second one covertly, and sell the ghost SIMs to fraudsters for profit.sentinelassam+2
Position in Fraud Chain
PoS agents act as the supply gatekeepers in the fraud ecosystem, providing anonymous SIMs that cybercriminals use to open mule bank accounts, make impersonation calls, and execute scams targeting victims in India and Southeast Asia. Downstream, these SIMs enable broader crimes like fraudulent UPI transfers and fake investment schemes, with telecom executives sometimes implicated in activations.medianama+2
Real Investigations
CBI’s 2025 FIR targeted 39 PoS agents across states like West Bengal, Uttar Pradesh, and Maharashtra for issuing 1,100 ghost SIMs linked to 2,200 cyber complaints, identifying 64,000 risky numbers overall. Mumbai police in 2026 scrutinized 54 agents after arrests in a racket supplying 100+ SIMs to international networks. Charges include identity theft under IT Act Sections 66C and 66D.mumbaimirror.indiatimes+2
The PoS Agent’s Role in the Fraud Chain
PoS (Point of Sale) machines are assigned to merchants and banking correspondents to enable card-based and wallet withdrawals. Rogue PoS agents exploit their access in two key ways:
Role 1: Mule Account Activation
Some bank-appointed Business Correspondents (BCs) open accounts for fraud networks using ghost SIM-linked KYC, bypassing in-person verification requirements. Per RBI inspection reports, compromised BCs are concentrated in states like Jharkhand, Bihar, and UP.
Role 2: Cash-Out Point
PoS machines are used to convert stolen digital funds into cash. Fraudsters make ‘purchases’ through the PoS using mule account cards — the PoS agent receives the digital credit, withdraws cash, and shares it with the fraud network minus their cut (typically 10–15%).
Ghost SIM Fraud Network: Geographic Hotspots
| State/Region | Primary Role in Fraud Chain | Known Fraud Operations |
|---|---|---|
| Jamtara, Jharkhand | SIM farming, mule accounts | Jamtara Fraud Syndicate (Netflix-documented) |
| Mewat, Haryana | Ghost SIM issuance, social engineering | OLX scam networks, KYC forgery |
| Mathura, UP | PoS cash-out networks | Banking correspondent abuse |
| Bharatpur, Rajasthan | Ghost SIM + UPI fraud | SIM rack operations |
| Nuapada, Odisha | Mule account operations | Impersonation networks |
| Pune/Mumbai urban areas | IT-enabled fraud, SIM swap | Corporate account targeting |
How Banks and NPCI Detect Ghost SIM Fraud
Velocity Rules
Banks monitor for unusual patterns — multiple accounts linked to the same SIM number, accounts receiving large inflows within days of activation, or accounts with sudden high-value withdrawals at PoS.
Device Fingerprinting
NPCI tracks device IDs associated with UPI transactions. If 20 different bank accounts are all operating from the same Android device IMEI, it is flagged for investigation.
Aadhaar Seeding Audit
RBI now mandates banks to audit Aadhaar-seeded accounts for multiple registrations. Automated CKYC (Central KYC Registry) cross-checks identify when the same Aadhaar has been used across more than a set number of accounts.
Telecom-Bank Linkage
TRAI and RBI have established a data-sharing framework: when a SIM is used to activate a bank account, both organisations are notified. Anomalies in SIM age, location, and activation pattern trigger joint alerts.
Real Example: How One Ghost SIM Network Was Dismantled
In 2024, a Pune-based cybercrime team traced a Rs 3.4 crore fraud to a SIM rack operation in Bharatpur, Rajasthan. The network had 340 ghost SIMs, 180 mule bank accounts, and 12 rogue PoS agents. The investigation took 8 months and resulted in 23 arrests — but only Rs 45 lakh was recovered, as most funds had moved to cryptocurrency and overseas hawala.
The case exposed a critical gap: by the time forensic labs extracted data from seized devices, the crypto wallets had been emptied and ghost SIMs discarded.
Comparison: Ghost SIM vs. SIM Swap vs. SIM Clone
| Method | How It Works | Victim Aware? | Bank Account Needed? |
|---|---|---|---|
| Ghost SIM | Fake KYC — victim never owns SIM | Usually not | Yes (mule account) |
| SIM Swap | Existing SIM ported with forged documents | Yes — loses signal | Uses victim’s own account |
| SIM Clone | Technical duplication (rare) | No | No — intercepts real OTPs |
Merchant Prevention Checklist: Avoid Becoming a PoS Mule
- Never allow unknown persons to ‘borrow’ your PoS machine — even briefly
- Verify every transaction reference against actual customer purchase before processing
- If approached to process ‘refunds’ for unknown parties, refuse and report to bank
- Inspect your PoS machine monthly for any hardware tampering or skimmer devices
- Report to your bank immediately if you see unusual high-volume PoS transactions you didn’t initiate
- Register on your bank’s merchant fraud alert programme — all major banks offer this
Eligibility for Fraud Recovery as a Merchant
- File complaint at cybercrime.gov.in and local police within 24 hours
- Provide PoS transaction logs, CCTV footage (if available), and customer details
- Contact your acquiring bank’s fraud team — not just general customer care
- NPCI has a dedicated merchant dispute mechanism via your payment service provider
Risks and Limitations
- Ghost SIM detection by banks is retrospective — fraud completes before flag is raised
- Rogue BC (Business Correspondent) prosecution is slow due to evidence complexity
- Crypto cash-out makes fund recovery nearly impossible after 6–12 hours
- Merchants can be inadvertently implicated as ‘money mules’ in PoS fraud — legal risk
Best Practices for the Ecosystem
- For telecom retailers: implement biometric re-verification for ALL SIM issuances — not just new connections
- For banks: daily reconciliation of PoS settlement against merchant profile — flag anomalies instantly
- For law enforcement: fast-track courts for cyber fraud to close the 8-month investigation gap
- For consumers: check your Aadhaar-linked SIMs at tafcop.dgtelecom.gov.in — report unknowns immediately
Frequently Asked Questions
| Q: What is ghost SIM fraud? |
| A: A ghost SIM is issued on stolen or forged KYC — the SIM exists but the ‘owner’ is unaware. It is used to receive OTPs for activating fraud bank accounts and authorising withdrawals. Checking tafcop.dgtelecom.gov.in shows all SIMs registered to your Aadhaar. |
| Q: What is the PoS agent’s role in cyber fraud? |
| A: Rogue PoS agents cash out stolen digital funds by processing fake ‘purchases’ through their machines, receiving digital credit, and withdrawing cash for the fraud network. They earn 10–15% of the amount processed. |
| Q: How do banks detect ghost SIM fraud? |
| A: Banks use velocity rules (multiple accounts per SIM), device fingerprinting (same device for multiple accounts), Aadhaar seeding audits, and TRAI-RBI data-sharing frameworks to flag ghost SIM patterns. |
| Q: Which states have the most ghost SIM fraud operations? |
| A: Jamtara (Jharkhand), Mewat (Haryana), Bharatpur (Rajasthan), Mathura (UP), and Nuapada (Odisha) are documented hotspots for SIM farming, mule accounts, and PoS cash-out operations. |
| Q: How can merchants prevent being used as PoS mules? |
| A: Never lend your PoS machine, refuse to process ‘refunds’ for unknown parties, verify every transaction against your own sales, and inspect hardware monthly. Report suspicious requests to your acquiring bank immediately. |
Conclusion
Ghost SIMs and rogue PoS agents are the invisible infrastructure that makes large-scale cyber fraud in India operationally possible. Without them, fraud networks cannot receive OTPs, activate mule accounts, or convert digital funds into cash.
Dismantling this infrastructure requires three things working in parallel: banks with real-time anomaly detection, telecom operators with biometric SIM issuance, and an empowered population that checks and reports ghost SIMs registered to their Aadhaar. Check your SIMs at tafcop.dgtelecom.gov.in today.
| Check all SIMs registered to your Aadhaar at tafcop.dgtelecom.gov.in — report any you don’t recognise. Merchants: contact your bank’s fraud team to join the merchant fraud alert programme. |